Note: Craig Schnarrs (@the_wifi_guy) does an great job of including a LOT of info on this amazing tool, the WLANPi. I appreciate his personal thoughts on the use of the tool and the included links so you do not have to hunt all over the web to find this info. Enjoy this great review of a wireless device that should be in your toolkit!

I’m always looking for ways to be more efficient in my job. One of my favorite low-cost tools is the WLAN Pi. This device was introduced to the community by Jerry Olla. It includes many tools for the wireless lan professional. It is a single board computer with a gigabit Ethernet interface that can push almost 900Mbps! This provides a great platform for testing throughput of both wired and wireless networks.

The operating system Armbian, a lightweight Debian Linux distribution, has great community support from respected Wi-Fi experts Nigel Bowden, Scott McDermott, Adrian Granados, Mike Kershaw and many others. The installation of the OS is very simple, download the image file from www.wlanpi.com and flash the image file to a microSD card using Balena etcher, https://www.balena.io/etcher/ (PC) or apple pie baker 2, https://bit.ly/2VFuOc1 (Mac).

The WLAN Pi supports the following wireless adapters

The micro-USB B port on the WLAN Pi supports the USB On-The-Go (OTG) specification. What this means is that when you connect your Mac or PC to the WLAN Pi using a USB to micro-B cable, the WLAN Pi appears in your Mac / PC as an Ethernet device, which is automatically configured via DHCP. The default IP address is 192.168.42.1. Once the unit is powered up, it will display its IP address on the LED.

If connected via Ethernet, enter the IP address displayed on the LED. Otherwise if connected via USB, use the address 192.168.42.1. The main menu is listed below along with a few of the tools for network performance testing.

The speed test menu

The speed test graph

Other included functionality
Network Performance Testing (iPerf2, iPerf3, and ePerf)
Kismet – wireless network device detector
H.O.R.S.T – Lightweight 802.11 wireless LAN analyzer
Scapy – packet manipulation program
TCPDUMP – CLI packet analyzer
Aircrack-ng – tools to assess Wi-Fi network security
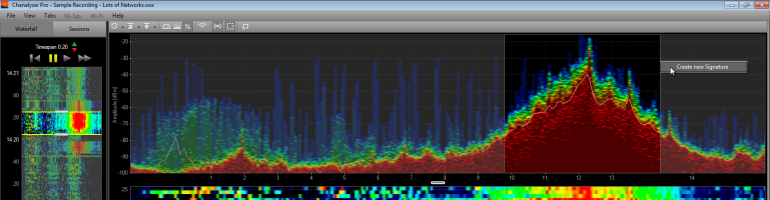
Wi-Fi Explorer Pro Sensor
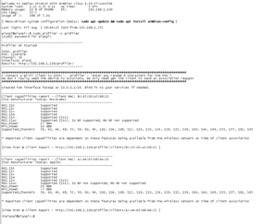
My favorite tool is the WLAN Pi profiler feature (by Nigel Bowden). https://github.com/WLAN-Pi/profiler
The profiler is based on a Python script to check wireless (802.11) capabilities based on association request frame contents. It has been developed to be specifically used with the WLAN Pi platform.
The script performs two functions:
- Create a “fake” access point that will broadcast an SSID of your choosing
- As clients attempt to join the SSID broadcast by the fake AP, it will analyze the association frames generated by clients to determine their 802.11 capabilities.
Understanding client capabilities is an important aspect of Wireless LAN design. It helps a network designer understand the features that may be enabled on a WLAN to optimize the design.
The capabilities supported by each client type may vary enormously, depending on factors such as the client wireless chipset, number of antennas, age of the client etc. Each client supplies details of its capabilities as it sends an 802.11 association frame to an access point. By capturing this frame, it is possible to decode and report on the client capabilities. One caveat, however, is that the client will match the capabilities advertised by an access point. For instance, if a 3 stream client detects that the access point supports only 2 streams, it will report that it (the client) only support 2 streams also.
To get around this shortcoming when trying to determine client capabilities, this script uses the Python FakeAP module to create a fake AP that advertises that it has the highest levels of feature sets enabled. This fools the client in to revealing its full capabilities, which are then analyzed from the association frame that it uses as it attempts to join the fake AP. It then uses the Scapy Python module to capture and analyze the association frames from each client to determine its capabilities.
A textual report is dumped in real-time to stdout and a text file copy is also dumped in to a directory of the WLANPi web server to allow browsing of reports. In addition, a copy of the association frame is dumped in PCAP file format in to the directory. Each result is also added to a summary CSV report file that is created for each analysis session when the script is run.
Community Support
One of the Most amazing things about the WLAN Pi is the amount of support from the Wireless LAN community.
Joel Crane created an external case for the WLAN Pi that looks really good.

http://www.potatofi.com/2019/10/the-wlan-pi-handheld-case.html
At the Wireless LAN Professionals conference there was a session on real world mobile testing using the WLAN Pi.
https://www.wlanpros.com/resources/wlan-pi-resources/
François Vergès has a great blog post on how to customize the WLAN Pi
https://www.semfionetworks.com/blog/customize-your-wlan-pi
https://www.semfionetworks.com/blog/wlan-pi-setup-a-wi-fi-hotspot
Adrian Granados wrote a Wireshark external capture interface / Plugin to perform live remote captures on a specific channel/channel width.
https://github.com/adriangranados/wlanpi-extcap.
How to setup the WLAN Pi as a sensor in Wi-Fi explorer Pro
https://www.adriangranados.com/blog/wlanpi-as-a-sensor
WLAN Pi the must have tool a blog by Scott McDermott
https://blogs.arubanetworks.com/solutions/a-new-tool-the-wlan-pi/
WLAN Pi Project | Jerry Olla | WLPC Phoenix 2019
https://www.youtube.com/watch?v=Nxx6varUwh0